Contrary to what a lot of modern films and Marvel television shows depict, the art of pickpocketing is fast becoming digital, as opposed to a shady man crouched in a dark foreboding alley. Our phones, for example, can be infiltrated remotely, with the sea of data stored within, including any shameless selfie photos, likely to be worth more than the contents of a wallet.
Even basic contact information, such as a phone number and email address, is valued at more than a small penny. Taking Instagram user information as an example, last week saw a bug expose millions of Instagram users’ contact information, including that of Selena Gomez (the horror!), to a group of hackers, who created a database which allowed anyone to search for a breached user’s contact information for just US$10.
Realising the potential of this growing threat was Tyler Harris, who cofounded of Armourcard, a product which protects cards with radio-frequency identification (RFID), or tap-and-go technology, from wireless hacking.
Previously working in the advertising and marketing space, Harris had a desire to start his own business, and began looking at areas of the market that could be disrupted. The entrepreneur came across RFID, a technology which was seeing an increased use in relation to products such as e-passports, etags and tap-and-go cards.
“I started hearing about how easy this technology is to skim. I did a bit of market research and saw there were a lot of passive methods, like wrapping cards in tin foil, used to protect items from wireless reaches – an almost archaic way in this technological world to stop a criminal,” said Harris.
Getting together with electrical engineers, Harris developed the technology for Armourcard, which functions by creating a 10cm microelectronic “force field” around a card or wallet to jam signals attempting to steal data from the RFID radio wave.
The product, which has been around for a number of years, is now sold both online and in bricks-and-mortar stores such as JBHIFI. To keep “ahead of the criminals”, however, the startup continued to conduct its research into cyber security.
Attending the inaugural International Consumer Electronics Show (CES) held in Las Vegas, Harris met with an ex-NSA employee, who honed down on an idea that was spread throughout the conference – that mobile phones would be the next area for criminals to target.
“Everything on there, photographs, contact information, app metadata, web browser data, can be accessed. Anything is worth something on the dark web,” said Harris.
The business has recently launched Armourcell, a smaller variation of the Armourcard, designed for mobiles. A peel-and-stick square, the Armourcell can be slapped onto the back of mobile phones to protect a user’s Near Field Communication (NFC) signal – the mobile equivalent of RFID – from wireless breaches.
“Criminals use the NFC signal, which works like RFID, to breach a device. It’s open to anyone; I can start skimming today with a free app for Google Play, for example,” explained Harris.
Of course, with NFC technology enabling the likes of tap-and-go phone payment apps, such as Samsung and Apple Pay, it’s not likely to go anywhere soon.
Describing Apple’s NFC tech as a “closed book”, however, Harris said that Android mobiles are currently exposed, thanks to the accessible NFC signal. Using this knowledge, the business tailored Armourcell to Android devices, using the power emitted from the NFC chip to power it rather than the actual phone battery.
As for how data is actually stolen off a device through NFC, the cofounder said the process is a lot like you’d expect, involving a hacker strolling by near a victim, stealing data without any physical contact.
“These criminals are doing a walk by. They’ve got a backpack connected to a laptop, which is often wired into a wireless router, pumping out a little code to the NFC feature of your phone,” Harris explained.
“It tells the phone that the next time it’s in a wifi zone, it should start backing up to the cloud, but the cloud destination is a trojan site, which is used by the criminal to take your data.”
Using a golden switch on the Armourcell, users are able to disable the jamming field so they can use their phone normally, with a small light in the centre of the product showing if the jamming effect is active.
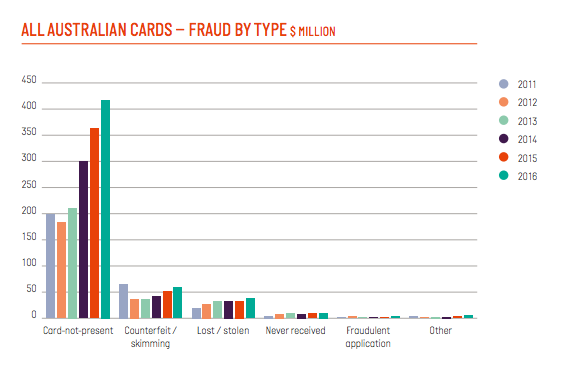
While the stats around “tap-and-go fraud” are still young, Harris said financial institutions are becoming increasingly aware and responsive to the issue. The last report, he said, attributed $40 million to tap-and-go fraud, although that number doesn’t account for all the victims who had money stolen without realising it.
Moreso, the statistic doesn’t account for the value of other data stolen from victims, such as contact information, photos and app metadata.
“Most people wouldn’t even know; it might only be $100 of your card one time, then they’ll move onto the next. We’re looking to protect people since this is what’s coming down the line, since this the next thing,” said Harris.
“In the future, it’s not even just about the money, it’s about identity theft. They’ll steal your name, photos, then everything else.”
According to the latest data from the Australian Payments Network (APN), previously the Australian Payments Clearing Association, card fraud resulting from skimming reached $59.2 million, a number which has gradually increased over the past few years.
Harris warned that other future products leveraging RFID technology, such as a Citizen Card, an ‘all-in-one’ legal identification card, will also be vulnerable on their release, posing further security and privacy issues.
“The tech is here to stay, and we as consumers need to start protecting ourselves. What’s worth most on the dark web, according to our source in the US, is images on your phone,” he said.
“Even apps you download can be trojans, by injecting certain commands into your phone when you accept the terms that pop-up when you start them. They can tell your phone to upload, say, card data from a payment app.”
Elsewhere in the cybersecurity space, a number of startups are working to tackle privacy issues and protect data.

SafeSwiss | Secure Code Warrior | ResponSight | UpGuard
With the aim of pushing Armourcell into bricks-and-mortar retailers, Harris said the business is currently in talks with local telecommunication companies.
To expand upon Armourcard, a number of other new features are in the pipeline, such as making the device rechargeable, linking it to an app, and adding an integration to Google Maps to show card skimming “hotspots”.
Image: Tyler Harris. Source: Supplied.

















Trending
Daily startup news and insights, delivered to your inbox.